Wire fraud is a growing risk, especially for multifamily and other commercial real estate investors. In 2021 alone, the FBI received 19,954 complaints of business email compromise (BEC) with an adjusted loss of nearly $2.4 billion.
Commercial real estate transactions can be particularly vulnerable to wire fraud because they happen on a regular and reoccurring basis and typically use established, straightforward processes.
Fraudsters have grown increasingly sophisticated. Many have learned the who, what and when of purchase transactions, including when investors and banks finalize loan documents and send deposits.
How wire fraud occurs
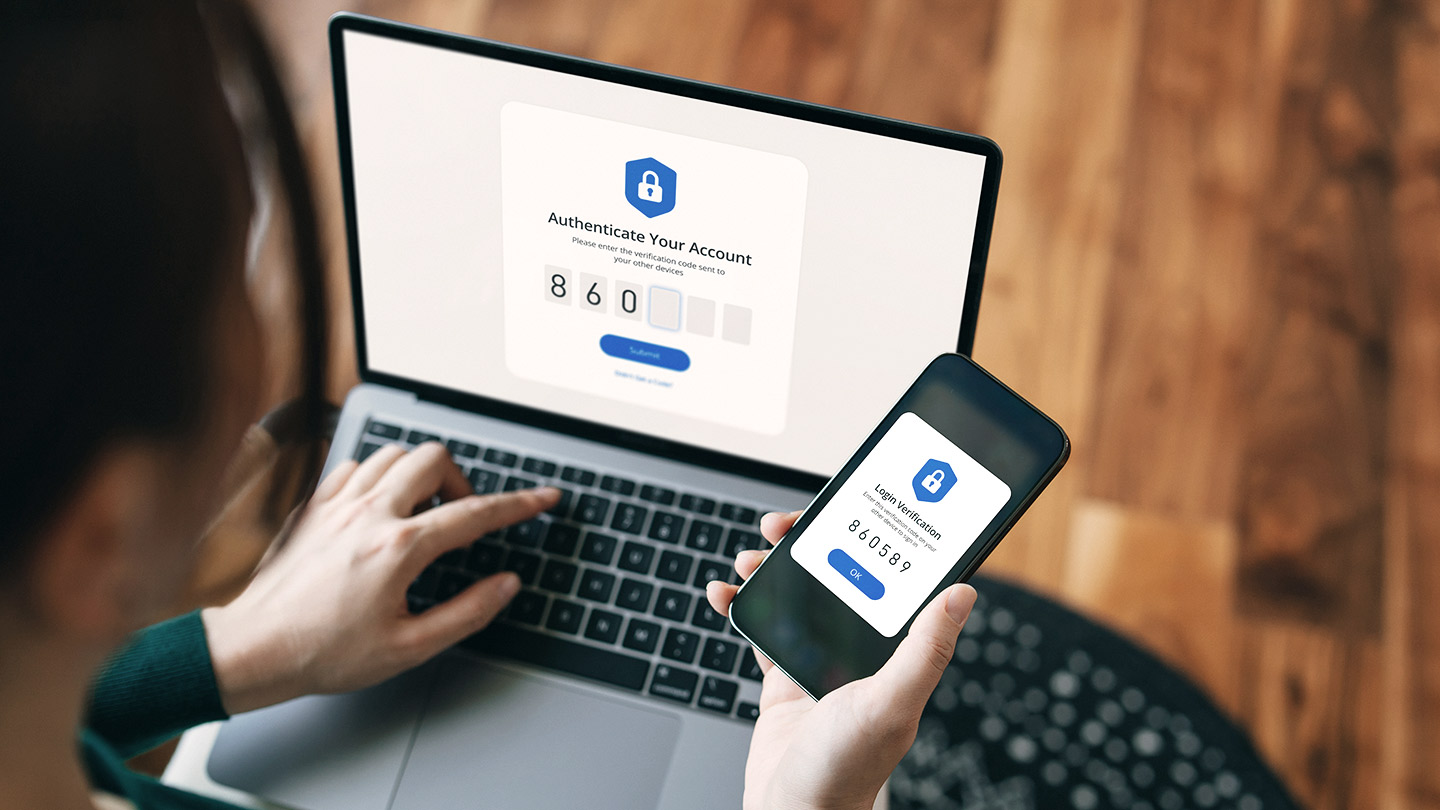
With multifamily transactions shifting online, there’s been an increase in phishing, a fraud method in which criminals attempt to impersonate reputable businesses or known parties through email. BEC is a form of phishing and among the most common types of fraud nationwide.
“BEC is a scheme in which criminals use email to trick a person into sending funds to an account controlled by the fraudster,” said John Geronimo, Executive Director and Fraud Strategy Director with Commercial Banking at JPMorgan Chase.
BEC is usually a three-step process:
- A criminal gains access to a known party’s email, referred to as an email takeover.
- The criminal monitors communications and waits until money is about to be moved.
- The criminal uses a compromised, authentic account or spoofed email address to impersonate the known party. The criminal then provides new instructions that direct the buyer to send funds to an account that the criminal controls.
“If the victim is the buyer, the spoofed email may appear to be from the escrow officer, the buyer’s real estate agent or even the buyer’s lender, requesting immediate transfer of the closing funds,” Geronimo said.
Commercial real estate wire fraud warning signs
Spotting red flags isn’t always simple. “Sometimes, the fraud attempt comes from a legitimate email address, and you just don’t know,” Geronimo said. “Even then, identifying that an ‘m’ has been replaced with ‘rn’ can be hard to spot if you’re not looking for it.”
But there are warning signs to look for, including:
- A change in wire instructions—it’s rare for any party to change banking information in the middle of a real estate transaction.
- Emails that demand urgent action, particularly those sent at the end of the month or the beginning of bank holidays.
- Outreach through multiple mediums, such as texts and phone calls, regarding the wire transfer.
- Emails sent outside of business operating hours.
- Grammatical errors or spelling mistakes within communications.
How to fight real estate wire fraud
“To protect against fraud, you really need a culture of vigilance,” Geronimo said. “It’s all about having internal controls and being able to deploy them effectively—many companies aren’t testing their controls and, as a result, employees aren't following them correctly or at all.”
To help protect against wire fraud, multifamily investors should:
- Understand the transaction process flow. Knowing timing and payment options (e.g., cashier’s check or wire) for finalizing closing funds is especially important.
- Always operate from a place of initial skepticism when receiving new instructions.
- Assume that emails—especially those asking for sensitive information or asking for transferring of funds—aren’t legitimate until they’re verified through a callback process.
The most effective step to take is conducting a callback. This involves using a phone number from a trusted system of records and calling to verify payment details or instructions. Never use a number sent in an email, as it could be the criminal’s—nor should an inbound call be blindly trusted in such situations.
The best way to ensure the funds are being sent to the appropriate account is by directly validating the instructions with the known party. But buyers shouldn’t rely on incoming phone calls claiming to be from the title or settlement company to verify the banking information. Fraudsters can easily use apps to manipulate their caller ID.
What to do if you experience wire fraud
For fraud victims, time is of the essence.
- Immediately contact the sending bank to request a recall due to fraud. The victim should also ask the sending bank to contact the receiving bank to request a freeze of the beneficiary account pending the recall.
- You also should file a report with the FBI Internet Crime Complaint Center.
- Contact law enforcement, including local police and the nearest FBI field office. You may want to reach out to law enforcement during regular business planning—knowing who to talk to and what you should do if a crime transpires ensures you’re prepared.
We’re here to help
With fraud on the rise, Commercial Term Lending’s team of local experts can help you get deals done swiftly and securely.
© 2023 JPMorgan Chase & Co. All rights reserved. JPMorgan Chase Bank, N.A. Member FDIC. Visit jpmorgan.com/cb-disclaimer for disclosures and disclaimers related to this content.