Government agencies are increasingly targets of cyberthreats as criminals try to steal or manipulate sensitive data.
Having a robust cybersecurity risk management plan is critical to helping your agency reduce exposure to threats. The key is to continually assess, refine and test your defense strategies. Even as threats evolve, there are four hallmark components that can serve as a foundation for your mitigation plans.
1. Make cybersecurity a priority
Managing cyber risk should be a priority for the highest levels of a government entity. The consequences of a breach—including those related to national security and election integrity—and the resource demands could be disastrous. Leaders should bring together the appropriate stakeholders to implement a holistic cyber risk management program.
2. Secure the weakest link
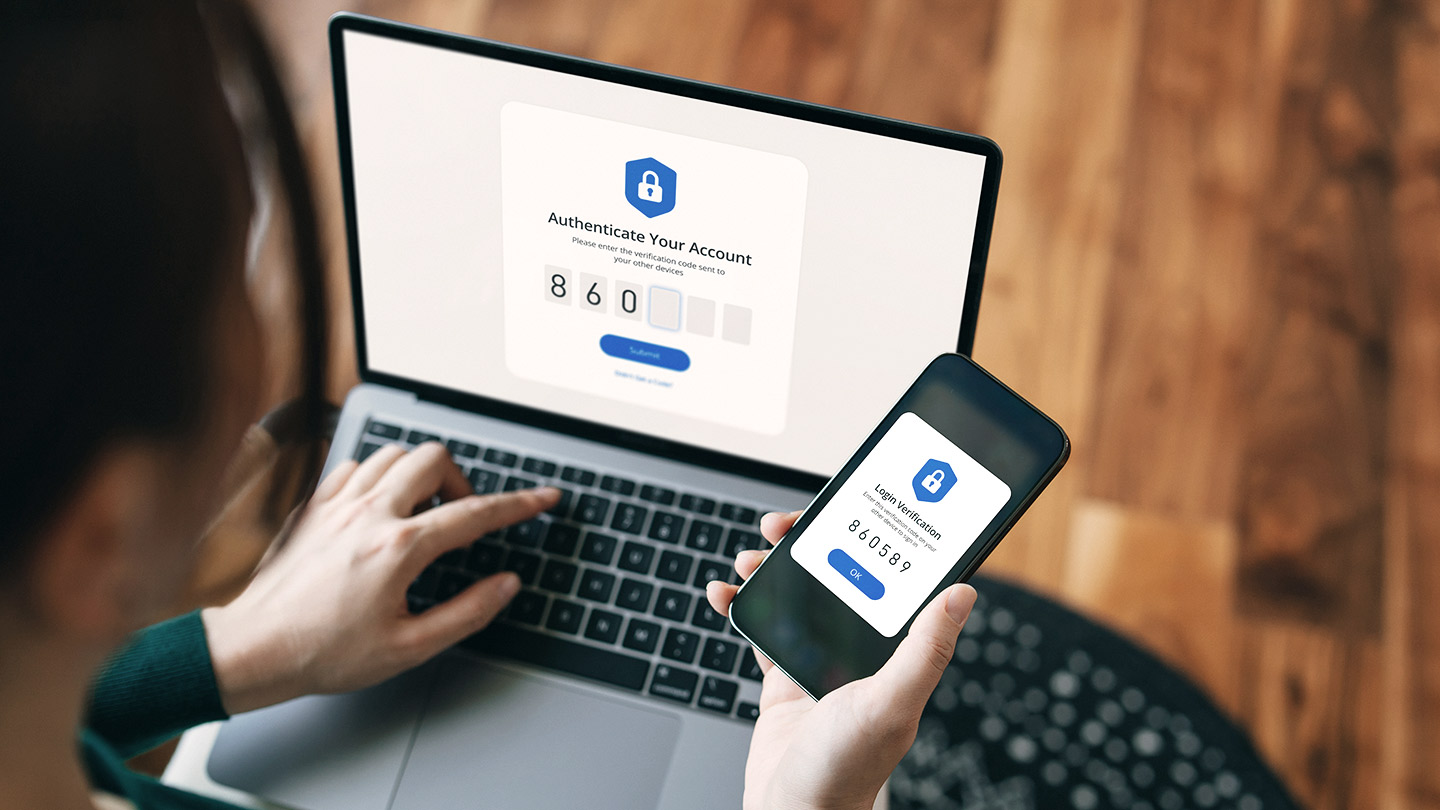
The weakest link in a cybersecurity chain is often the employee using a computer or mobile device connected to the organizational network. Regularly perform exercises with staff to keep them updated on cyberthreats and how they should respond.
The more regularly employees are tested, and the more robust their training, the more diligent they will be. Fraud awareness training for employees helped the Kentucky State Treasury team quickly stop a $5.3 million business email compromise scheme.
Of those surveyed as part of the Sophos whitepaper The State of Ransomware in State and Local Government 2022:
- Nearly 6 in 10 state and local government agencies were targeted by ransomware in 2021, a 70% increase from 2020. About three-quarters of those saw the attack successfully encrypt data.
- The average ransom payment for a successful attack on a state or local government was more than $200,000.
- For those that experienced a ransomware attack, the average recovery and remediation cost was $660,000 per government entity.
Sophos Ltd, The State of Ransomware in State and Local Government 2022, Sept. 19, 2022
3. Build a culture of cyber preparedness
The Cybersecurity Capability Model (C2M2) is a tool to help organizations evaluate and improve their cybersecurity efforts.
One essential resource in this effort is the National Institute of Standards and Technology Cybersecurity Framework (CSF). The CSF and its affiliated self-assessment toolkit help organizations set benchmarks, identify priorities, implement risk management tactics, measure improvement and adopt appropriate changes. Using this approach, government entities can help drive their preparedness to a level that can meet the current threat landscape.
4. Enlist third-party expertise
Government entities—particularly at the state and local level—may not always have sufficient in-house resources or budgeting to fully implement cybersecurity tactics. Supplementing your operations with third parties can help provide added security capabilities. Should a breach occur, third parties can:
- Help conduct capability, risk, vulnerability and impact assessments
- Scan networks for threats and provide corrective actions
- Develop strategy by applying industry knowledge
- Provide rigorous, ongoing training and awareness initiatives
Financial institutions typically have insights, tools and the experience to help protect your online systems and other networks from cyberattacks. Whenever possible, lean on your financial partners to help provide education and awareness training, share best practices and mitigation strategies—or to test your organization’s cybersecurity preparedness.
We're here to help
JPMorgan Chase is dedicated to fighting cyberattacks, and we have a number of tools, products and resources to help protect your business. Talk to your relationship team about how we can help you mitigate cybersecurity risks.
© 2022 JPMorgan Chase & Co. All rights reserved. JPMorgan Chase Bank, N.A. Member FDIC. Visit jpmorgan.com/cb-disclaimer for disclosures and disclaimers related to this content.