For Companies and Institutions
-
Commercial Banking
We provide tailored credit, financing, treasury and payment solutions for businesses of all sizes and commercial real estate. Backed by the strength and stability of J.P. Morgan, our dedicated experts deliver industry-specific guidance and services, empowering you to manage cash flow, seize growth opportunities and achieve your strategic goals.
-
Global Corporate Banking
We help clients achieve their long-term strategic goals through financing, liquidity, payments, risk management and investment banking solutions.
-
Investment Banking
Providing investment banking solutions, including M&A, capital raising and risk management, for a broad range of corporations, institutions and governments.
-
Payments
Your partner for commerce, receivables, cross-currency, working capital, blockchain, liquidity and more.
Key Links
For Institutional Investors
-
Asset Management
Putting our long-tenured investment teams on the line to earn the trust of institutional investors.
-
Markets
Direct access to market leading liquidity harnessed through world-class research, tools, data, and analytics.
-
Securities Services
Helping institutional investors, traditional and alternative asset and fund managers, broker dealers and equity issuers meet the demands of a rapidly evolving market.
-
Global Research
Leveraging cutting-edge technology and innovative tools to bring clients industry-leading analysis and investment advice.
-
Prime Services
Helping hedge funds, asset managers and institutional investors meet the demands of a rapidly evolving market.
-
Global Liquidity Solutions
Global short-term fixed income strategies designed to help clients manage liquidity through the cycle.
Key Links
For Individuals
-
Wealth Management
With J.P. Morgan Wealth Management, you can invest on your own or work with an advisor to design a personalized investment strategy. We have opportunities for every investor.
-
Private Bank
A uniquely elevated private banking experience shaped around you.
For Employers
-
Workplace Solutions
Enhance your equity compensation offering with solutions designed to empower your employees and bring your reward strategy to life.
Key Links
Who We Serve
Key Links
Explore a variety of insights.
Key Links
Insights by Topic
Explore a variety of insights organized by different topics.
Key Links
Insights by Type
Explore a variety of insights organized by different types of content and media.
Key Links
We aim to be the most respected financial services firm in the world, serving corporations and individuals in more than 100 countries.
Key Links
- Insights
- Payments
- Payments Security & Trust
- Add an extra level of security to sensitive payment data with tokenization

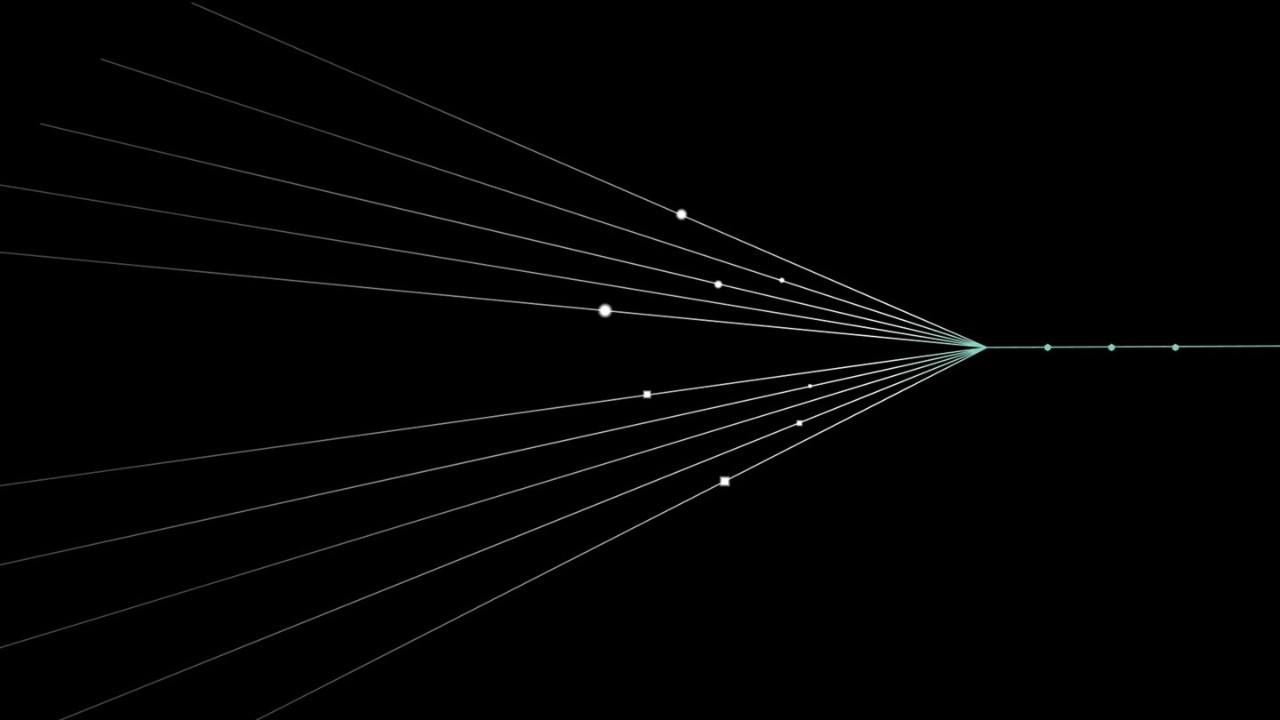
How tokenization and encryption work together
Card-present transactions
-
Customer’s card data is encrypted and formatted at the point of sale.
-
An algorithm reformats the data so the POS system processes it in the same manner as previously unencrypted data.
-
Encrypted data is transmitted to our system, decrypted and processed through the payment brand networks.
-
We reply with a token for future use.
Card-not-present transactions
-
Customer purchases from your website.
-
Data encrypted within your website.
-
Our server decrypts card data to process payment.
-
We reply with a token for future use.
Key Benefits
- Help protect customer payment data from fraud both within and outside your network.
- Reduce the risk of card data exposure in the event of a data breach.
- Minimize the impact of Payment Card Industry (PCI) scope by not storing and transmitting cardholder data.
- Maintain business processes that rely on cardholder data.
Related Insights
Unlock the power of Hosted Payment solutions
Learn how we deliver exceptional security for eCommerce by contacting your J.P. Morgan representative today.
Related insights

Payments
May 20, 2026
Learn how BILL helps businesses manage payments in real time with an API-based sub-ledgering solution.
Payments
From friction to flow: How public and private chains are fueling the new financial physics
May 12, 2026
Explore how private and public blockchains are rewriting the rules of finance with atomic settlement, tokenized assets and institutional-grade solutions from Kinexys.

Payments
How embedded payments can unlock SaaS growth in the AI era
Apr 30, 2026
Embedding payments does more than help your clients transact. It creates a competitive edge by making your software platform indispensable and unlocking new revenue opportunities.

Payments
Unum streamlines and protects important insurance payments with J.P. Morgan
Apr 29, 2026
Learn how Unum simplified payments and achieved Nacha compliance with J.P. Morgan Concourse™.

Payments
Payments Outlook: Five shifts powering payments
Apr 23, 2026
Explore five trends shaping payments, from real-time liquidity and AI-powered fraud defense to blockchain settlements and personalized experiences.

Payments
Driving advanced cross-border payments for ABA Bank
Apr 23, 2026
Discover how Xpedite, Wire 365 and Principal Protection solutions from J.P. Morgan helped ABA Bank enhance its cross-border payments services amid rapid customer growth.

Payments
Six infrastructure fronts reshaping fintech payments
Mar 18, 2026
Infrastructure investments across payments, fraud detection, AI and networks form an interconnected system. Smart sequencing creates compounding advantages rather than isolated wins.

Payments
5 payments trends to watch in 2026
Mar 06, 2026
Shifts in the payments landscape create new ways for businesses to unlock efficiencies, deliver value for their organization and better serve customers. J.P. Morgan Payments has identified five key trends to explore in 2026 and beyond, from technological innovation to evolving consumer expectations and growing fraud risks.
You're now leaving J.P. Morgan
J.P. Morgan’s website and/or mobile terms, privacy and security policies don’t apply to the site or app you're about to visit. Please review its terms, privacy and security policies to see how they apply to you. J.P. Morgan isn’t responsible for (and doesn’t provide) any products, services or content at this third-party site or app, except for products and services that explicitly carry the J.P. Morgan name.