Fraudulent card testing has emerged as a growing threat due to COVID-19 driving a significant increase in online and mobile transaction volume. Relatively difficult for some merchants to detect, unmitigated card testing attacks can be very expensive – increasing transaction costs, reducing valid authorization performance and potentially exposing merchants to additional fraud.
A fraudulent card testing attack begins with fraud actors acquiring stolen partial or full card credentials. The fraud actor will then use various digital tools, including bots or scripts, that can rapidly submit hundreds of thousands of card-not-present (CNP) transaction authorization requests on an e-commerce site. If left undetected, this can result in thousands of dollars of fees for declined transactions.
The fraud actor’s main objective is quickly identifying a valid card and/or revealing a card’s missing security elements. With valid card credentials, they can then proceed to make fraudulent large ticket purchases on the targeted merchant’s website or at other online merchants.
Common indicators of card testing
Key indicators of fraudulent card testing include an unusually high card authorization volume for low dollar amounts in rapid succession, high identical authorization request volume, a sharp increase in declines and specific decline codes and finally a big increase in issuing bank/payment brand authorization mismatches.
"No single factor can prevent card testing fraud, however, a multilayered approach can help merchants prevent card testing fraud attacks."
Una Ryan Kearns
VICE PRESIDENT OF FRAUD, J.P. MORGAN
Mitigating a card testing attack in progress
Merchants that have identified ongoing card testing activity can use internal data analytics to change defined rule logic in their fraud solution to combat the attack. If the majority of declines are coming from the same card number, then it is probable that the fraud actor has the correct card number and is testing to identify the security elements. In this case, the merchant should immediately block the card.
Similarly, if the card testing attack shares the same email, phone, IP address and device ID, then these customer attributes should be blocked. When blocking an IP address or device tag, it is vital to verify that this action will not impact false positives.
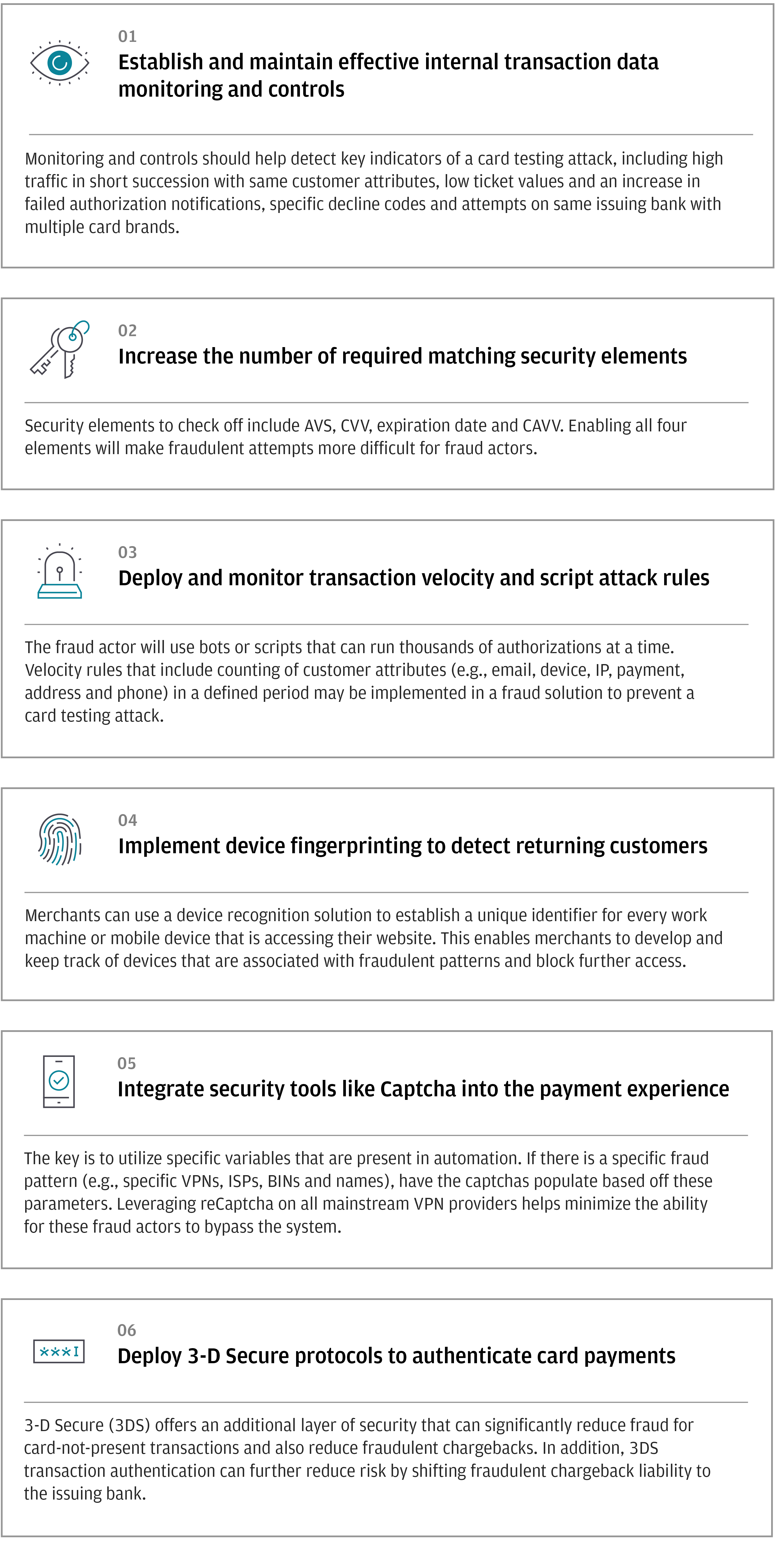
Here are six ways to help prevent card testing attacks
Una Ryan, Vice President of Fraud, J.P. Morgan
Una Ryan is Vice President of Fraud in J.P. Morgan Merchant Services Data & Analytics group. Una has more than 10 years of international fraud mitigation experience that spans merchant, fintech and acquiring segments. Her areas of expertise include PSD2 fraud regulations, consultancy in fraud detection and rule management, chargebacks/disputes and card-not-present fraud insights.
Need a turnkey fraud solution? Safetech Fraud Tools delivers.
J.P. Morgan’s Safetech Fraud Tools seamlessly integrates J.P. Morgan transaction processing expertise with Kount’s scalable fraud detection platform. This powerful fraud mitigation solution features multi-layer device fingerprinting, proxy piercing, dynamic order linking, dynamic risk scoring, custom rules management and auto-decisioning.
Safetech's Identity Trust Global Network and machine learning algorithms can immediately alert merchants of signs of card testing attacks. Best of all, Safetech can be implemented quickly and rapidly provide e-commerce fraud protection.
To learn more, please contact your J.P. Morgan representative.