Ransomware
Stay informed about the growing threat of ransomware, cybercrime and fraud. Explore articles and insights from J.P. Morgan experts on threat prevention, detection and effective responses.
For Companies and Institutions
Key Links
For Institutional Investors
Putting our long-tenured investment teams on the line to earn the trust of institutional investors.
Direct access to market leading liquidity harnessed through world-class research, tools, data, and analytics.
Helping institutional investors, traditional and alternative asset and fund managers, broker dealers and equity issuers meet the demands of a rapidly evolving market.
Leveraging cutting-edge technology and innovative tools to bring clients industry-leading analysis and investment advice.
Helping hedge funds, asset managers and institutional investors meet the demands of a rapidly evolving market.
Global short-term fixed income strategies designed to help clients manage liquidity through the cycle.
Key Links
For Individuals
For Employers
Enhance your equity compensation offering with solutions designed to empower your employees and bring your reward strategy to life.
Key Links
Who We Serve
Key Links
Explore a variety of insights.
Key Links
Insights by Topic
Explore a variety of insights organized by different topics.
Key Links
Insights by Type
Explore a variety of insights organized by different types of content and media.
Key Links
We aim to be the most respected financial services firm in the world, serving corporations and individuals in more than 100 countries.
Key Links
Stay informed about the growing threat of ransomware, cybercrime and fraud. Explore articles and insights from J.P. Morgan experts on threat prevention, detection and effective responses.
All topics
No results found
Adjust your filter selections to find what you’re looking for

Cybersecurity
BEC busters: Four callback do’s and don’ts
Feb 27, 2026
Callbacks help prevent payments fraud, but the process isn’t foolproof. Here’s how to protect yourself from business email compromise.

Cybersecurity
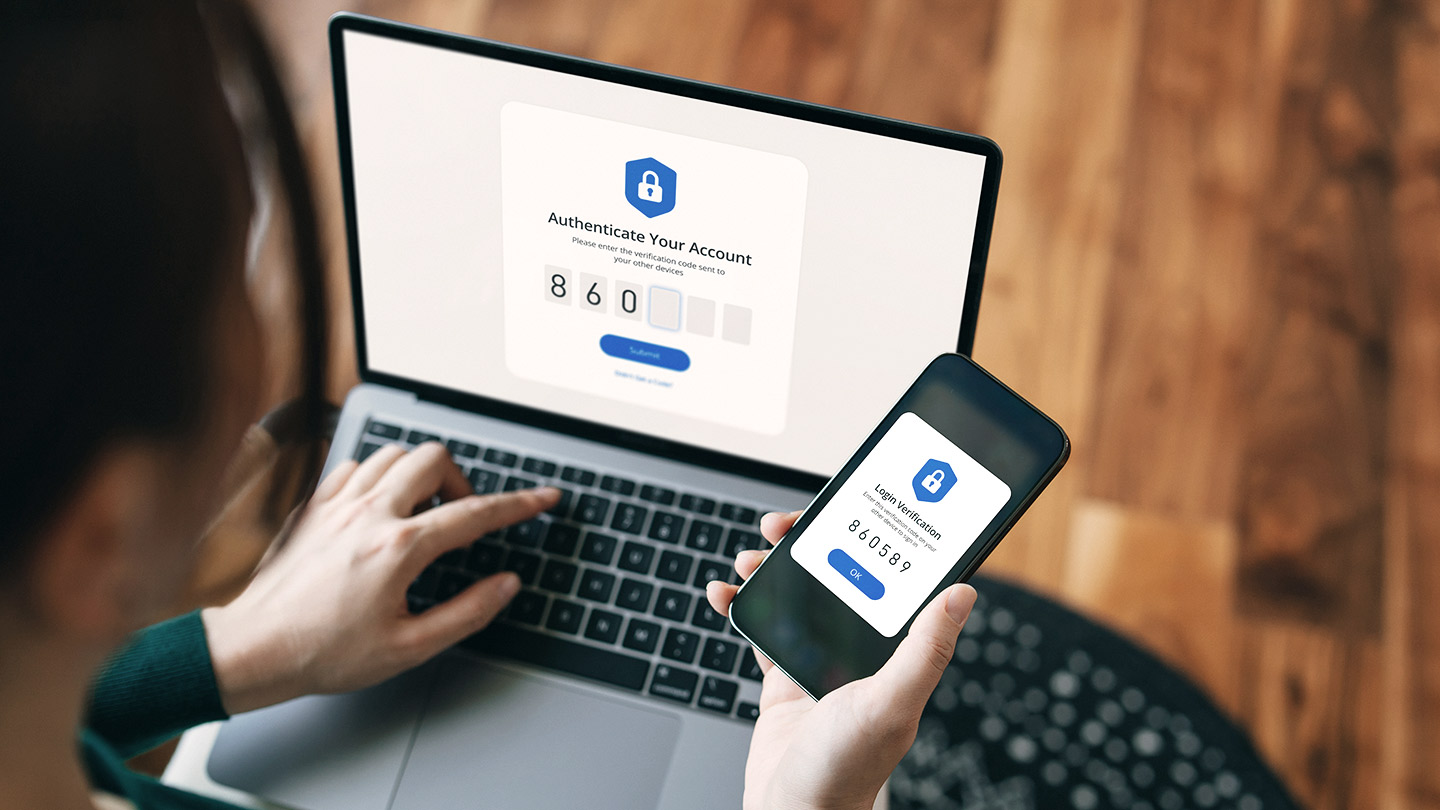
3 cyber secure actions to add to your New Year’s resolutions
Jan 23, 2026
New year, new emerging cybersecurity threats. These tips will help keep your digital presence under lock.
Cybersecurity
Protect your business: Spot fake emails and websites
Jan 22, 2026
Spotting small changes in web addresses and emails can help you avoid scams and keep your business safe from online threats.

Cybersecurity
AI-powered scams: How you can help protect yourself
Dec 02, 2025
Fraudsters are now using AI to put a new, sophisticated spin on age-old scams, making personal and financial security more vital than ever. Learn what you can do to help protect yourself.

Cybersecurity
Your house may be spying on you. Save yourself.
Oct 27, 2025
All the smart devices embedded in our homes can put us at risk. Discover how to secure your IoT devices, and what you can do to protect yourself.

Cybersecurity
Parents, you need to teach your kids about financial fraud
Oct 23, 2025
With the increasing complexity of fraud schemes, it’s important your kids understand how to keep their accounts and personal information safe.

Cybersecurity
The social media seesaw: How family guidelines balance sharing with security
Oct 01, 2025
As individuals’ and families’ profiles and finances increase, so does their likelihood of becoming targets of cybercrime and facing reputational damage. Learn more here.

Cybersecurity
Unmasking social engineering: Protecting your wealth from deceptive cyber tactics
Oct 01, 2025
Social engineering is a powerful tool used by cybercriminals to manipulate individuals into revealing sensitive information, using tactics such as phishing, artificial intelligence and more. Discover how to recognize and thwart these tactics.
You're now leaving J.P. Morgan
J.P. Morgan’s website and/or mobile terms, privacy and security policies don’t apply to the site or app you're about to visit. Please review its terms, privacy and security policies to see how they apply to you. J.P. Morgan isn’t responsible for (and doesn’t provide) any products, services or content at this third-party site or app, except for products and services that explicitly carry the J.P. Morgan name.