Having a robust cybersecurity risk management plan is critical to help your organization reduce exposure to cyberthreats. Business leaders must continually update, refine and test their cybersecurity defense strategies to combat risks such as ransomware and business email compromise (BEC).
To help organizations fortify existing plans, the National Security Agency (NSA) has a list of recommendations and best practices for mitigating cyberattacks.
These 12 cybersecurity strategies can serve as a foundation for your mitigation plan and strengthen your security protocols. We have identified who should perform these duties so you can get the right people involved.
1. Update and upgrade software
Who: Director of Information Technology (IT)
Apply all software updates as soon as they are available. Ideally, you should automate this. Cybercriminals can engineer exploits almost as soon as a patch is released. Many vendors offer update services that can help with automation; just be sure to use updates delivered through protected links and to test them prior to production release.
2. Limit and control account access
Who: Human Resources (sets policy), Director of IT (executes)
Threat actors gather account credentials, so it’s recommended that you start your program with a zero-trust framework. Under this model, account privileges are assigned sparingly only as users need them. Have documented procedures for securely resetting credentials or use a privileged access management tool to automate credential management. Also, update your onboarding and offboarding procedures to align with a zero-trust approach.
3. Enforce signed software execution policies
Who: System Administration
Your operating system should protect itself using a secure boot—a capability that ensures devices boot using only secure software. To do this, enforce signed software execution policies for scripts, executables, device drivers and system firmware. Allowing unsigned software can give cybercriminals an entry point.
4. Formalize a disaster recovery plan
Who: Business Operations, CFO/Treasury and IT Management
Crafting a disaster recovery plan (DRP) is key to effectively mitigating cyberattacks. Your plan should start with business continuity and address data protection, data restoration, offsite backups, system reconstitution, configurations and logs. Remember, a DRP is not a static document; it should be continuously reviewed and updated. Building periodic reviews into your overall cybersecurity risk management plan will help identify any gaps.
5. Actively manage systems and configurations
Who: IT Administration
Regularly scan and take inventory of your network devices and software. Remove unnecessary or unexpected hardware and software from the network. Such hygiene contributes to cyber risk mitigation by reducing the attack surface and establishing control of the operational environment.
6. Hunt for network intrusions
Who: Security Operations and/or Third-Party Penetration Testers
Operate under the assumption that a compromise has occurred and take proactive measures to detect, contain and remove any malicious presence. Automated tools like endpoint-detection and response solutions should be paired with hunt operations and penetration testing. Such steps can evolve your cybersecurity defense strategies beyond basic detection methods and toward real-time threat detection and remediation.
7. Leverage hardware security features
Who: System Administration
Contemporary hardware security features built into modern computers can increase system integrity. Schedule older devices for a hardware refresh, or at the least, use an updated operating system on outdated hardware. This can help better protect systems, critical data and user credentials from threat actors.
8. Segregate networks using application-aware defenses
Who: Network Administration
Cybercriminals can hide malicious activity and compromise data over common protocols that transfer data across networks. Application-aware mechanisms, like firewalls, can restrict certain applications if found to be compromised. Start by segregating critical networks and services, then deploying network defenses to block improper traffic and restrict content.
9. Consider using threat reputation services
Who: Third-Party Service
Cyberthreats emerge rapidly, often occurring faster than most organizations are equipped to handle. A third-party threat reputation service takes information globally to detect and correlate threats in real time. This can improve your cyber risk mitigation by increasing coverage of threats, vulnerabilities and trends.
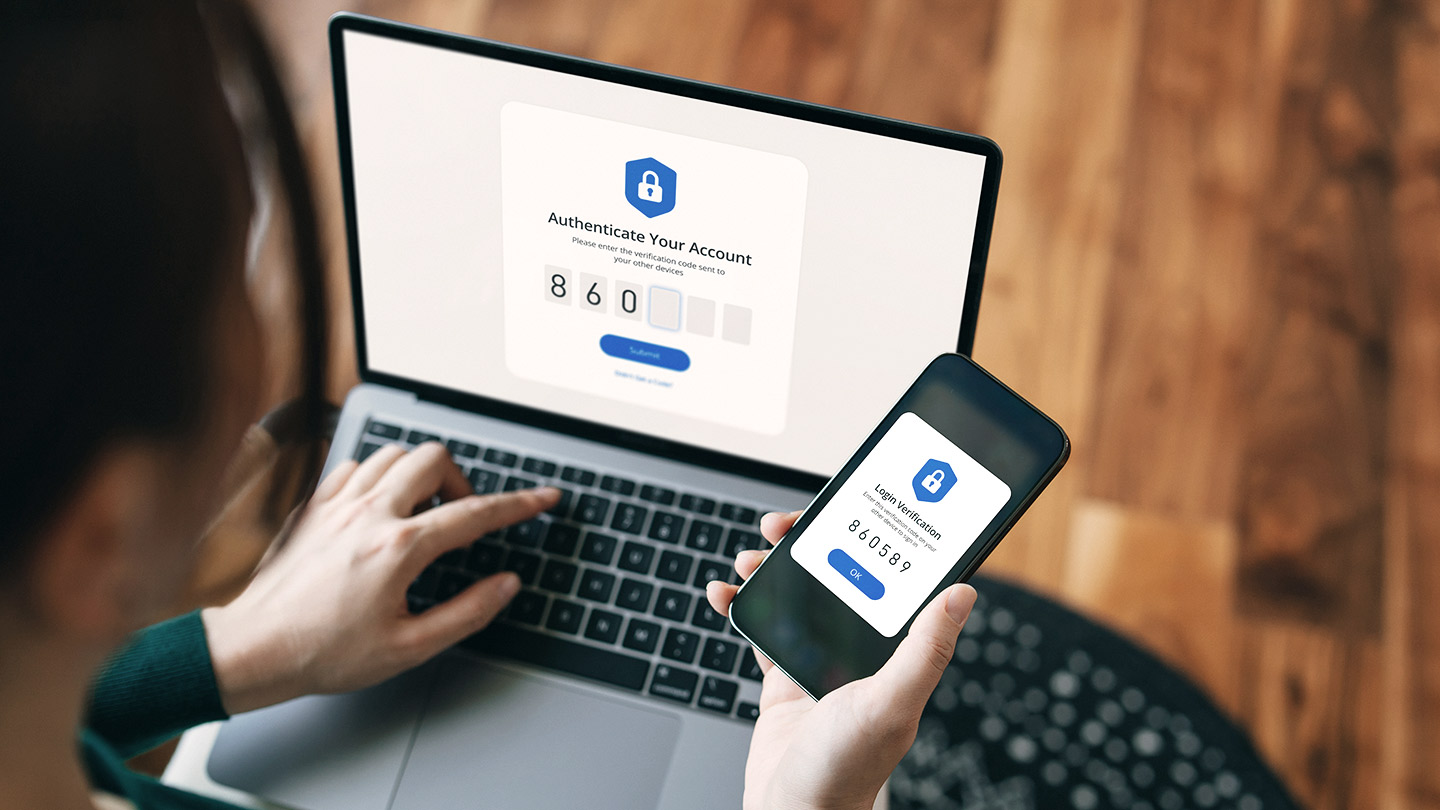
10. Leverage multifactor authentication
Who: IT Manager/Administration
Multifactor authentication is a necessity for mitigating cyberattacks. Use this protection for accounts with elevated privileges, remote access and/or containing high-value assets. Physical token-based authentication systems should be used to supplement knowledge-based factors such as passwords and PINs.
11. Monitor third-party security posture
Who: Security Operations
Vendors, third-party suppliers and clients that do business with you present a unique set of security risks. External partners often have access to your organization’s sensitive data or support essential business processes. It’s critical that you continuously monitor third-party risks and properly assess partner cybersecurity plans to help secure your assets.
12. Assume insider threats exist
Who: Business Operations
Insider threats occur in various forms, ranging from intentional misuse of system access and confidential information to inadvertent errors like clicking on a phishing email. Consider adopting a layered approach for addressing insider threats, including regular assessments and ongoing employee training and awareness campaigns.
- There is no way to completely ensure you will not be a victim of ransomware or another cyberattack, so heightened diligence and ongoing review of controls with your internal and external partners is of paramount importance.
- As new threats emerge and technology advances, your organization will need to be proactive in applying new defensive strategies and using the latest tools.
- Contact your Commercial Banking relationship team to learn more about how to mitigate cybersecurity risks.