Key takeaways
- Effective cybersecurity is only accomplished through a shared responsibility between the public and private sector. Active safeguards need to be treated as a top priority for all organizations, no matter their location, size or business type.
- Contact your Commercial Banking relationship team to discuss how we can help in your security efforts.
In a June 2021 message for corporate executives, the White House urged the business community to take immediate steps to secure private networks as cybercriminals continue disruptive ransomware attacks on utility companies, food processing plants, schools, hospitals and governments. This call to action from the White House speaks to the growing threat these attacks pose to every organization’s core operations, no matter the size, location or industry.
The memo followed President Biden’s May 2021 executive order that requires the federal government to improve and protect its own networks and systems. In the message for the private sector, the administration called for similar precautions.
“Maintaining the security for one business requires a shared effort with others in the community,” says Anne Davis, Head of Cyber and Technology Controls for Commercial Banking with JPMorgan Chase. “With the escalation in attacks, it’s important for each organization to review and fortify its security controls to avoid falling victim to a ransomware attack.”
The growing risk of ransomware needs to stay top of mind for the leaders of any organization.
“Ransomware must be viewed as a threat to an organization’s core business—not simply as a potential issue, but as a real and constant threat,” says Christopher S. Huttleston, Security Specialist with JPMorgan Chase. By identifying cyberattacks as a priority concern, executives can look at where to invest resources, time and effort on cybersecurity prevention and recovery strategies.
“There needs to be a very clear plan that’s created at the C-suite level for what you’re doing about ransomware, and the awareness should be shared with the board of directors,” he says.
Here are six ways your organization should take action to mitigate risks and strengthen existing defenses.
1. Follow the federal government’s lead.
The White House’s executive order only governs systems within the U.S. government, but it provides a framework for any organization to implement quickly.
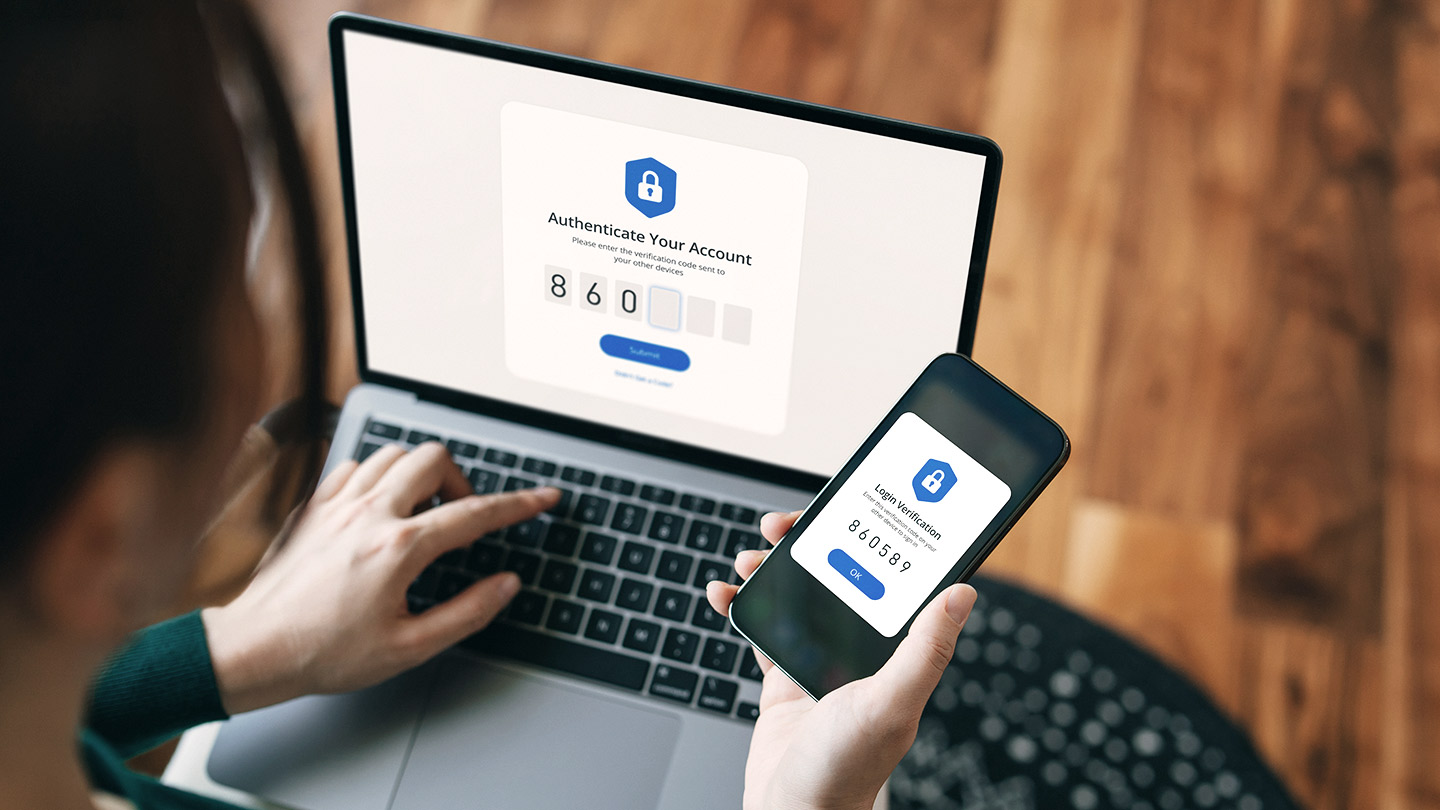
- Multifactor authentication. Requiring an additional factor, like a one-time password, token or key, is a safeguard in case a username-password combination is compromised.
- Endpoint detection and response (EDR). EDR systems continuously scan the inbound and outbound traffic on your network to identify suspicious activity and isolate the concern before it spreads, alerting you to investigate further.
- Encryption. Consider using encryption to make data harder to access, copy or transfer.
- A security team. Empower your staff to establish preventive measures to defend your network.
2. Test your backups.
Regularly maintained backups of your systems let you restore quickly after an attack. Maintain your backups offline so they can’t be deleted or locked by hackers. And test them regularly so you’re confident they work before an emergency arises.
3. Stay updated.
Hardware and software are constantly being patched to limit security flaws. Make sure your security team is installing the latest updates on your devices. Use a risk-based strategy to help prioritize critical system updates to remediate potential vulnerabilities that may be exploited by cybercriminals.
4. Test the response plan.
Just like businesses practice drills for fires, lockdowns and natural disasters, management plans will expose gaps in your response, resiliency and recovery plans before it’s too late. Play out scenarios to determine how long you can sustain business operations and payment processes if certain systems are down.
5. Use a third party to simulate an attack.
Hiring a third party specializing in security testing will help you identify opportunities to uplift your security by following the same aggressive tactics that cybercriminals use. In return, you’ll learn about the unsecured entry points to your system. Costs for testing typically scale with the size of a business.
6. Break it up.
Ransomware attacks are increasingly posing risks not only to corporate systems but also operational networks. Filter your internet access to control traffic between different parts of your network and be ready to isolate parts of your network so it can continue to operate even if you are under attack. Segment privileged accounts, like administrator accounts, from those used for day-to-day tasks.