
You’ve already invested in cybersecurity and fraud prevention training for your employees to enable them to spot business email compromise and other fraud schemes. While your employee education can help strengthen cyber awareness and foil some attacks, there may be other payments fraud schemes that your organization could overlook.
Many small and midsized offices have limited staffing, oversight or controls and rely on a small group of trusted employees to process payments. Fraud can happen to any business—whether it’s perpetrated by an employee or an external threat. It’s important for management to establish proper policies and procedures for payment processing, such as requiring dual approval to safeguard the release of funds, regardless of the payment method.
Nearly three-quarters of businesses that used checks reported they were targets of attempted and/or actual payments fraud last year, according to the Association for Financial Professionals Payments Fraud and Control Survey. The survey also reported that checks accounted for 42% of business-to-business payments.
Your check contains sensitive account information that can make your organization vulnerable to fraud. Have you thought about the opportunities for a criminal to commit fraud throughout a check’s life cycle?
Check Life Cycle
Once a check is picked up, there are multiple opportunities for the fraudster to potentially intercept a payment.
-

OUTGOING MAIL
After a check is issued in your office, it’s generally dropped in the outgoing mail for pickup.
-

MAIL EN ROUTE
The check travels through several stops before arriving at the recipient’s office.
-

INCOMING MAIL
Once there, the check is either delivered to the payee directly or may sit in an individual mailbox for pickup.
How Fraudsters Can Use Account Information
Once the fraudster obtains your account information, they can use it to alter checks and send fraudulent payments:
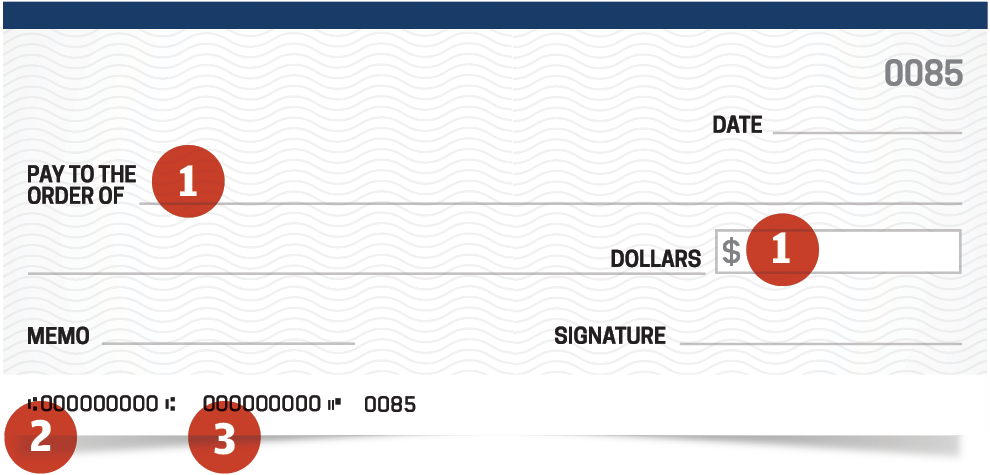
1. Payee and Dollar Amount
By using acetone or other chemicals, fraudsters erase or wash checks and then replace the payee name or alter the dollar amount.
2. Checking Account Number
Newer technology allows fraudsters to create counterfeit checks using check stock and add your stolen account number.
3. Account and Routing Number
Fraudsters use the account and routing number to make electronic payments, such as a utility bill or online purchases. The payments will often be in small denominations that may go unnoticed but add up quickly. If you notice fraudulent activity on your account, report it immediately to your financial institution.
Check Fraud Controls
JPMorgan Chase recently launched a new, self-enrolled digital hub to help small and midsized clients better protect their businesses and manage money safely with these enhanced fraud prevention tools:
Check Protection Services (Connect) or Positive Pay (J.P. Morgan Access®): When you issue checks, you provide issuance details to the bank and then confirm or decline payment for things that don’t match your issuance information, such as the payee name, amount and check number.
Check Monitoring (Connect) or Reverse Positive Pay (J.P. Morgan Access®): This process allows you to establish a specific amount threshold so any checks that exceed that amount are presented to you for payment confirmation.
Post No Checks (PNC): Completely block any fraudulent checks from posting to accounts that do not issue checks. If you do not write checks against your account, PNC will block a check from being cashed against your account. Consider consolidating check writing to one bank account and adding PNC to the remaining accounts. Contact your Client Service Representative to set up PNC.
ACH Fraud Prevention Tools
Your organization can set up additional ACH fraud prevention tools to help protect your accounts from electronic fraud:
Cashflow360SM: Digitally automate and streamline your billing, payments and invoice processes, making them simpler and more secure. Allow your vendors to manage their own ACH payment information and outsource your check print services to securely print and mail checks. When you limit exposure of your account information by using electronic payment options, you limit the opportunities for misuse.
ACH Debit Block: Specify which ACH debits can withdraw money from your account. This can be customized by amount and vendor as well as set user entitlements to limit which employees can set or change these rules. If someone does get hold of your account information, the block will stop any unauthorized electronic debits to your account.
Get in Touch
Prefer to talk directly to one of our experts?







